In the previous Blockchain Design Course module we talked about blockchains – the technology that underlies Web3. These are sometimes referred to as Layer 1 protocols. Blockchain protocols defines how nodes communicate, and come to consensus, with each other in order to form a functioning cryptonetwork. Everything is centered around the cryptonetwork’s native Web3 token. In this article we will about about Web3 tokens in general: both utility and security tokens, as well as fungible and non-fungible tokens. Web3 tokens change the game as far as open-source software development goes – the future is bright! This article is an extension of the Web3 Design Course 2022.
By the way – there’s also a video version of this article (see below).
Billions Rely on Internet Protocols Everyday
Software protocols have been crucial in the development of information technologies. Billions of users everyday rely on internet protocols to access the web. These internet protocols dictate how networked computers request and share information with each other. Let’s take a look back at how these protocols developed, and where we are currently in terms of the development of the internet as a whole.
The internet is simply a network of connected computers. Once computers are physically connected in a network, software protocols standardize how these computers share data with one another. This includes rule sets for locating other computers on the network, sending data packets to a desired location, and checking that messages were received and correctly interpreted. These internet protocols can be broken into four layers:
- Hardware protocols
- Internet Protocol (i.e. IP)
- Transmission Control Protocol (i.e. TCP)
- Application Protocols (e.g. HTTP)
Hypertext Transmission Protocol (HTTP) is an important application protocol. HTTP defines how a computer requests data from, and serves data to, another computer. A common example is for a computer to request an HTML file from a web server (using an HTTP GET request) in order to view a web page on its internet browser.
This HTTP GET request then gets passed down one layer to the Transmission Control Protocol (TCP), which tells the computer how to break the message into smaller data packets that will be sent one by one to the web server. TCP is also used by the web server receiving the data packets in order to assemble the data packets back into the original message.
The Internet Protocol (IP) ensures that the data packets reach their intended destination. Before sending the HTTP GET message via TCP, the IP wraps data packets with an IP address corresponding to the web server. This is like the “To:” field on a mail envelope. Finally, hardware protocols convert the data packets into electrical signals that get transmitted through the internet’s physical infrastructure (e.g. cables, modems, routers).
On the other end, the web server will send back an HTML file using the same HTTP and TCP/IP process described above. Now you have a rough idea of how the web functions with a set of open-source internet protocols. These protocols were developed by independent researchers and non-profit organizations, and haven’t been modified much since the mid-1990’s. All of the web products we enjoy today would not exist without these internet protocols.
The Internet is Still Evolving
This is a good point to talk about the evolution of the internet. We can break the internet’s development into three phases: Web1, Web2, and Web3.
Web1 is characterized as “read-only” because only a few entities published content for consumption by many. The internet was thought of at this time as a digital encyclopedia. Users accessed static web pages containing text, images, and hyperlinks; however, there was little interactivity for end-users other than consumption.
This brings us to Web2, which is also referred to as the “social web”. Online communities and identities began to emerge at this time. Web2 is especially characterized by social media platforms, and the idea of user-generated content. Now everyone had the ability to create content, build a social network, and react to the posts of others (e.g. like and share buttons). The web went from a few content creators to billions. If Web1 is considered “read-only” then Web2 can be considered “read-write” for the average user. Centralized web platforms attracted users with large networks and simple user experiences.
This has ended in a winner-take-all dynamic. There are several monopoly-like companies, such as Google, Amazon, Apple, and Facebook, that largely control how the internet is experienced by end-users. For example, users must agree to the terms and conditions of these centralized companies if they want to participate in the dominant social network. Also, Web2 companies have the rights to all the user data generated on these platforms, which they mine and sell to advertisers. Roughly 98% of Facebook’s revenue is generated in this way. It’s a strange idea that we’ve become accustomed to – that users who join a network, and increase the value of that network with their presence and activity, capture little, if any, of the value they create.
Additionally, large user bases act as an economic moat that protect Web2 companies from competition, making these platforms cautious of third-party development, and product integrations. This incentivizes Web2 companies to close-off their ecosystems, which stifles innovation. For example, Apple is able to reject applications from launching on its app store for any number of reasons, one of which being competitive risk. And, even when it accepts applications, Apple takes a hefty 30% cut from the application’s revenues. Of course, third-party developers are paying for the privilege to launch on a platform with a reach of over 1 billion iOS users. Still, one wishes for something better than a system that extracts value from its end-users, and regards third-party development coolly, if not with open-hostility.
To recap, going from Web1 to Web2, we went from open-source internet protocols, intended to decentralize information sharing, to monopoly-like, centralized social networks that limit end-user choice, and third-party integrations. Web3 can remedy the current issues with Web2. Web3 users can literally self-custody their data, identity, and other digital assets with cryptographic wallets. And, developers can now choose to build applications on neutral, open-source Web3 platforms (i.e. blockchains). Web3 removes rent-seeking middlemen and connects users directly to the applications they want to use. If things change, they can pick up, and move to another ecosystem that better suits their needs, without the loss of data or other digital assets.
One of the major innovation’s of Web3, and something important to wrap your head around as a Web3 product designer, is that Web3 aligns incentives better than the current system. Developers, end-users, and cryptonetwork service providers (i.e. nodes) are all incentivized to work towards the same goal – the growth of the cryptonetwork. This is all made possible by Web3 tokens.
The Role of Web3 Tokens
We’ve discussed in previous modules of the Blockchain Design Course that tokens native to a cryptonetwork incentivize nodes to secure, and maintain, that cryptonetwork. These nodes can be thought of as network service providers. They dedicate their resources to provide a decentralized blockchain database for dApps to build on top of, and are rewarded with that cryptonetwork’s native token.
Additionally, native tokens are staked by these nodes to ensure that they act according to the best interest of the cryptonetwork. This secures the cryptonetwork from attack because stakes can be slashed. The cryptonetwork is also protected from denial of service attacks by requiring users to pay for their usage of the cryptonetwork with its native token. This makes spamming the network with unnecessary transactions prohibitively expensive.
In other words, the native token coordinates, and incentivizes, globally distributed, independently-acting nodes to maintain the blockchain, while at the same time protecting it from attack. This is all kind of complicated. You may notice this is unnecessary in the world of Web2 because companies cover the cost of the centralized databases their applications run on. But, as we already talked about in the previous section, there are hidden costs with centralized gatekeepers who have unilateral control over the platform, and its data. Simply put, tokens make possible the decentralized, open, and neutral properties of Web3.
Think back to what we learned about internet protocols. They were developed over 30 years ago by independent researchers and non-profit organizations, and haven’t changed much since. In the beginning, before the enormous commercial value of the internet was realized, it was difficult to get funding to build out the protocols. Now, protocol developers can create a cryptonetwork and hold on to a portion of the native token. If the protocol provides value, and is adopted, then the token price will increase in value, because the token is required to use cryptonetwork in the first place (see above). Also, the founding team can sell off some of the tokens to fund initial, or ongoing, development. Thus, Web3 tokens provide a direct value capture, and funding, mechanism for open-source protocols.
This brings us to the next point – Web3 tokens help bootstrap cryptonetwork adoption. Remember, networks are proportional in value to the number of users in the network. Facebook is much less compelling with only 100 users, and AirBnB just isn’t that useful with only 100 hosts. So it’s difficult to get things off the ground; however, cryptonetworks can reward its early-adopters – whether that be developers or end-users – with its native token. If the network succeeds then the early-adopters profit greatly, rewarding them for the value they provided to the network early on. Also, now that they are token holders, and have a financial stake in the network, early-adopters are incentivized to help grow the network through word of mouth, or social media promotion.
Think about the internet as divided into two layers: the protocol layer (e.g. HTTP, TCP/IP, etc.) and the application layer (e.g. Facebook, Instagram, etc.). In Web2, all of the value accrues to the application layer, which has led to some of the most valuable companies in the world today. Remember there was no effective way to capture value from open-source protocols until Web3 tokens came along.
The fat protocol thesis posits that value will consolidate at the protocol layer in the Web3 era. As dApps, built on these Web3 protocols, go mainstream and attract hundreds of millions of users, the protocol’s native token will increase in value. This is because the native token is required to use the dApps – a classic example of utility tokens, discussed in the next section. An increase in token price signals a growing ecosystem, which will attract more developers to build out additional functionality on the blockchain, which will attract more end-users. Web3 tokens are responsible for positive feedback loops like this.
As mentioned before, internet protocols have not changed much since their initial release back in the 90’s. There were efforts to make modifications, but it was too difficult as there was no clear ownership over the protocols. Now, cryptonetworks are beginning to build governance, and upgradeability directly into the protocol. Token holders can vote on protocol improvement proposals. The more tokens they have the more their vote counts. Some believe this is unfair, especially when individual users hold a disproportionately large share of the protocol’s token; however, it is important to point out that the more token you hold, the more financial stake you have in the protocol. All token holders are incentivized to vote for the good of the protocol because the token value can appreciate or depreciate depending on the outcome.
In this section we talked about many of the dynamics brought about by Web3 tokens. To summarize, Web3 tokens get distributed to all cryptonetwork stakeholders: protocol developers, third-party dApp developers, end-users, and network service providers. This is why cryptonetworks are sometimes referred to as “community owned and operated” networks. Everyone in the cryptonetwork is aligned to the same goal – for the cryptonetwork to grow and prosper so that the value of the token increases. This is vastly different from the misalignment characteristic of the current Web2 system.
Web3 Token Categories & Use-Cases
In the previous section we talked about the role played by tokens native to cryptonetworks. As you may have heard there are literally thousands of Web3 tokens in existence today – some native to cryptonetworks, and some launched on top of these cryptonetwork. This vast token landscape can be broken into two high-level categories: utility tokens and security tokens.
Utility tokens are by far the most common Web3 token. These tokens are used to access cryptonetwork services. Ether is a good example of a utility token, because it is used to pay for using the Ethereum blockchain. In other words, users pay ether to Ethereum nodesfor processing their transactions. All smart contract blockchains have a native utility token like this. Ethereum is a general purpose cryptonetwork that can run all sorts of dApps; however, there are other specialized cryptonetworks. Just as an example, Sia and Golem are cryptonetworks that provide decentralized cloud storage and cloud compute, respectively. Users of these cryptonetworks redeem SiaCoin (SC) and Golem Network Tokens (GNT) to utilize these decentralized services.
The other major category is security tokens. Securities in the traditional finance world include things like stocks and bonds. Organizations issue securities in order to raise capital, whereas investors purchase securities with an expectation of some return over a period of time. These investment vehicles are regulated by the SEC in order to protect investors from fraud and ensure fair, efficient markets. Security tokens are registered securities that are transacted on the blockchain for faster and cheaper settlement, and more transparency compared to traditional markets. Organizations have already begun issuing stocks and bonds on Ethereum. Other security tokens are backed by real-world assets like precious metals (PAXG), commodities (XPD), and real-estate (IHT).
Notice the difference between utility tokens and security tokens when it comes to regulation. Security tokens play by the rules of traditional capital markets and willingly undergo government regulation during their launch; whereas, issuers of utility tokens claim that their tokens are not securities and, therefore, do not need to comply with securities regulations. The SEC, led by Gary Gensler, largely disagrees with this claim – he says the vast majority of “utility tokens” appear to him as unregistered securities. This is one of the great tensions between the US government and Web3 at the moment, and we’ll see later in this article.
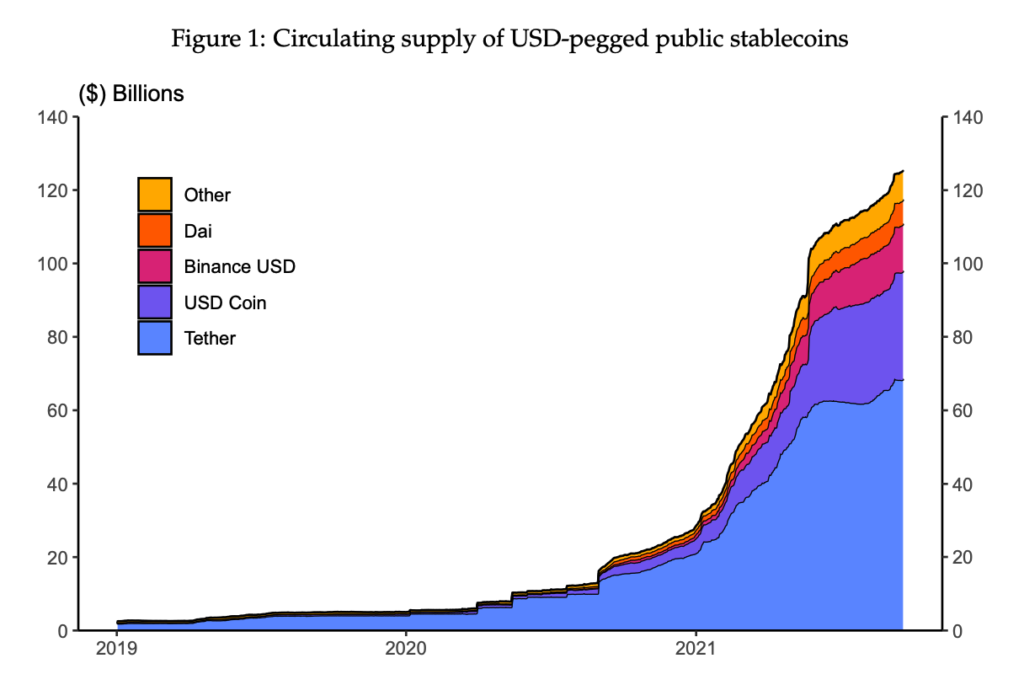
It’s difficult to place stablecoins in either of these token categories, but they deserve an honorable mention as they grow more and more popular. These tokens are designed to maintain a stable value over time. This makes stablecoins more attractive as a medium of exchange compared to other Web3 tokens that experience high price volatility. Usually, stablecoins are pegged in value to a fiat currency like the US Dollar. For example, the two most popular stablecoins – USDC and USDT – are fully-backed by US dollar reserves held in traditional financial institutions. These are called fiat-collateralized stablecoins; however, there are other emerging stablecoin categories such as crypto-collateralized (e.g. DAI), and algorithmic stablecoins (e.g. OHM).
Now, let’s go back to utility tokens. There are many sub-categories of utility tokens, and it’s difficult to fit any one token into a single category – they usually belong to multiple categories at once. Below I list some other use-cases of utility tokens, nost as an exhaustive list, but to give you a flavor of the experimentation that is being done on token design.
- Governance: Allows users to submit, and vote on, improvement proposals for protocol upgrades. They first came onto the scene with some of Ethereum’s popular DeFi protocols (i.e. Compound, MakerDAO, and Uniswap). These DeFi protocols distributed their governance tokens to their users, effectively decentralizing the governance of the protocols. Now token holders have significant influence over the evolution of the protocol, not just the core development team.
- Cashflow: Earn a portion of the protocol’s revenues – this is often called “staking”. For example, most smart contract blockchains allow users to stake the cryptonetwork’s native token, and earn block rewards for doing so. Also, UNI token holders receive a portion of the swap fee that Uniswap charges for facilitating token swaps.
- Discounts: This is a common use-case on crypto trading platforms. For example, holding CEL token gives users preferential interest rates when lending/borrowing on Celsius Network, and BNB and FTT get users discounted trading fees on Binance and FTX, respectively.
- Gaming: Most Web3 games have in-game currencies that can be redeemed for in-game items. For example, virtual animals can be bred with one another using SLP token in Axie Infinity. Also, MANA is consumed in oder to generate land plots in Decentraland’s metaverse.
- Social/Community: The most obvious use-case here is with social media influencers who launch a token backed by their own reputation (see Rally). Social tokens give patrons a direct way to support celebrities, influencers, and artists while enjoying additional benefits like access to exclusive content, entrance into in-person events, access to private online communities, and more.
So these are the Web3 token categories, and some of their use-cases. Let’s now talk about token launches, and some of the problems associated with token launches. We’ll eventually get into the regulatory issues surrounding Web3 tokens.
Web3 Tokens as Real-Time VC Investments
All Web3 tokens have a pre-defined monetary policy controlled by the blockchain. For example, is it an inflationary or fixed-supply token? And if it’s inflationary, what’s the token’s issuance schedule? This monetary policy is fixed, and cannot be changed once the token has been launched.
As we’ve seen, most cryptonetworks have their own native utility token, which powers the network; however, smart contract blockchains give anyone the ability to launch their own token, defined by its own monetary policy and programmed with arbitrary utility. This led to an explosion of new Web3 tokens on Ethereum starting in 2017. Now tens of thousands of Web3 tokens exist across various cryptonetwork ecosystems.
Web3 projects often publish a website and a whitepaper that explains the team’s motivation and approach. This inevitably leads to a discussion about the Web3 project’s token, specifically its monetary policy and token distribution plans. Let’s say a blockchain launches with a fixed supply of 1 billion tokens. Pie charts often illustrate how these tokens will get distributed to project stakeholders. For example, a portion of the tokens are sold to public, and/or private investors, to fund the development of the project. This crowdsale is called an ICO, or initial coin offering. Other tokens are usually distributed to the founding team, the project’s treasury, or adjacent foundations.
Web3 tokens also democratize venture capital investing. Up until now, investing in early-stage startups has only been available to accredited investors through Series A, B, and C funding rounds. The 1000x gains already have been realized by the time retail investors have the opportunity to invest. Also, typically, VC investments are illiquid – after the funding round, it often takes years for the startup to find product market fit so that seed investors can realize a profit. Web3 tokens change the game. They are like highly liquid venture capital investments, with real-time price feeds, sometimes before the project launches.
So far, Web3 tokens have been successful at funding the development of Web3 ecosystems, but let’s now talk about some concerns, starting with the obvious one: scams. Anyone can launch a token and sell it on the open market. In the past, people have launched tokens without a legitimate project backing it. Scammers create intriguing marketing content and hype it on social media to create demand for their token, without any intent on building a product in the first place. When others start buying the token, the token price goes up, and the scammers dump their token supply on the open market. The token price then crashes, and the original investors are left holding a worthless scam token with no legitimate project backing it. This is called a “rug pull”.
Token launches themselves present their own problems. Who has access to the token’s crowdsale? Does the token get distributed to many individual retail investors? Or, are the crowdsales just available to big-money, private investors like VCs. If VCs, or the founding team, hold a large portion of the cryptonetwork’s token supply, then this calls into question the true decentralization of that cryptonetwork. Some argue that this is no longer a neutral, decentralized network, but one that is controlled by a large minority.
There is an alternative to crowdsales – something known as a “fair launch”. Satoshi launched the Bitcoin protocol in 2009. There was no crowdsale of pre-allocated bitcoin. Bitcoin nodes just started mining bitcoin, and the circulating supply of bitcoin grew from there. Yearn Finance, a popular DeFi protocol, is another example of a fair launch. It distributed 30,000 YFI tokens to early-adopters of the Yearn Finance protocol in what is called a “token airdrop”. Juxtapose these fair launches to other Web3 projects with token pre-allocations and crowdsales. The diagram above shows how Layer 1 smart contract blockchains distributed their initial token supply.
Perhaps from the perspective of Web3’s ethos – that of decentralized inclusivity – fair launches are preferred to public crowdsales, which are preferred to large token pre-allocations to private investors, founding teams, and adjacent foundations. I’m not trying to pass judgment here – it’s a complex issue that founding teams are experimenting with. Token launch is one thing, but the sustainability of the project over decades is another. The SEC definitely takes a stance on this. Anything other than a fair launch appears to the SEC as the sale of unregistered securities, which they intend on regulating over the next several years.
Looming SEC Regulation of Web3 Tokens
The SEC determines whether or not something is a security with the Howey Test, a precedent set by the Supreme Court lawsuit between Howey Company and the SEC back in 1946. Howey Company operated a hotel with an adjacent orange grove. The company started selling plots of the orange grove to its hotel guests. The owners of these plots would have rights to a portion of the revenues generated from the orange grove. Howey argued this was the sale of real-estate; however, the SEC argued this was the sale of a security and won the Supreme court case, thus establishing the definition of a security. Something is considered a security if it is:
- An investment of money
- In a common enterprise
- With the expectation of profit
- To be derived from the efforts of others
Clearly, according to the Howey Test, the crowdsale of Web3 tokens constitute a securities offering that requires SEC regulations in order for US investors to participate. But what is the purpose of SEC regulations, and what does it mean for Web3 tokens moving forward? The SEC cares about protecting US investors from fraudulent activity, and wants securities markets to operate fairly and efficiently. Security token issuers must make disclosures to reduce information asymmetries between the issuer and the investor. Also, the SEC would be able to hold fraudulent token issuers accountable, like the scam tokens discussed in the section above.
The downside is that there will be much more friction when it comes to launching security tokens. Launches will take longer while waiting for SEC review, and will cost more due to the increase in legal overhead. Also, this token regulation will likely make it more difficult for retail investors to get the same exposure to early-stage Web3 investments as they currently enjoy in the wild-west of ICOs. Some security token frameworks have been established to simplify the process of regulated token issuance – see SAFT to learn more.
However, the Howey Test was established back in the 1940’s, and many Web3 evangelists believe that securities laws are too outdated to handle Web3 tokens. They argue that the regulatory framework needs modification to effectively handle emerging digital assets. An example of this is Hester Peirce’s Safe Harbor proposal, which allows for unregulated token issuance as long as the Web3 project decentralizes ownership and governance of the protocol within three years from launch.
The proposal takes advantage of the fact that an asset can change from a security to non-security over time. In other words, an asset that starts off as a security offering, may eventually change so that the Howey Test no longer classifies the asset as a security. On several occasions, the SEC has alluded that this is their view on Ethereum. Ether started as a security offering with its public crowdsale; however, the token has been distributed across so many independent actors that Ethereum can no longer be considered a “common enterprise”.
Last thing to say, there are regulatory bodies, other than the SEC, that have a stake in Web3 technologies. These include the Fed, Treasury, CFTC, OCC, CFPB, and FDIC. As Ryan Selkis points out in his annual crypto report, currently these entities range from neutral to openly opposed to Web3. There is still much to be determined in terms of regulation. Regulatory outcomes are sure to affect the growth and evolution of Web3 around the world. It’s unclear at this point how it will all play out; however, some jurisdictions are trying to attract Web3 entrepreneurs and businesses with more welcoming dialogue and regulation. Foreign countries like Switzerland, Germany, and Portugal, as well as US states like Wyoming, Texas, and Florida are among some of these Web3-friendly havens.
All the Web3 tokens mentioned thus far are “fungible” tokens. Fungibility exists in the real-world, with fiat currency being a good example. One paper dollar bill is equivalent in value to another paper dollar bill. Fungible tokens are the same way: one bitcoin is equivalent in value to another bitcoin; however, non-fungible tokens serve vastly different purposes. In the next section, we’ll give a background on non-fungible tokens and discuss their varied use-cases.
Non-Fungible Tokens (NFTs) & Cryptomedia
Again, let’s start with the concept of fungibility. Fungibility means that an item can be replaced by another equivalent item. Currency is a good example of something that is fungible. One ten dollar bill is the same as another ten dollar bill. Even though the bills were printed at different times, in different locations, on different pieces of paper, we still consider them equivalent to one another, because they are fungible. Fungibility just means that an item can be replaced by an equivalent item.
Most things in the real-world, however, are non-fungible. People are non-fungible. The family heirloom, passed down to you by your grandparents, is non-fungible. The Mona Lisa, hanging in the Louvre in Paris, is non-fungible. And your life memories are non-fungible.
Now, let’s take this concept of “fungibility” back into the digital, Web3 world. Bitcoin is fungible because one bitcoin is equivalent to all other bitcoins. Currently, most digital content is fungible. Think of image, video, and audio files – we can infinitely replicate them, and share with thousands of people, effectively for free, with the click of a button; however, thanks to non-fungible tokens (NFTs) we can now make digital files rare, or “scarce”, for the first time ever. And just like fungible tokens, anyone is free to launch NFTs on public blockchains. This is known as “minting” NFTs. Whereas fungible tokens have a token supply, all NFTs are unique, and distinct from one another. They are 1 of 1.
One of the first major use-cases for NFTs has been one-of-a-kind digital art. Now, patrons can purchase digital art as NFTs, and custody the NFT in their Web3 wallets. 2021 was a big year for NFTs with over $17B worth of NFTs transacted. And some of these NFTs have demanded seemingly outrageous prices for digital art. A collage by a well-known artist Beeple, sold for $69 million dollars – this was the most expensive NFT ever sold, and the third highest price ever paid for work by a living artist. Check out these other popular artists making millions of dollars from their NFT sales.
When first learning about NFTs, most people don’t understand why someone would spend millions of dollars, or any money for that matter, to purchase a jpeg that is publicly accessible. Indeed, the Beeple NFT can be viewed, downloaded, and shared by anyone. This is known as the “right-click save” misconception. The true game-changing power of NFTs is that ownership of the original Beeple NFT can be proven. Whoever purchased this NFT now custodies it in his/her Web3 wallet, and anyone can verify this ownership because it is a public record on the Ethereum blockchain.
Another NFT-related phenomenon is PFP, or profile-picture NFTs. These are collections of NFTs, usually depicting avatars that vary based on attributes like background, jewelry, clothing, and other accessories. The two most popular PFP collections are Crypto Punks and Bored Ape Yacht Club (BAYC). Passionate communities have sprung up around these NFT collections, and membership isn’t cheap. For both collections, a total of 10,000 unique avatars were minted, and the cheapest BAYC NFT is currently selling for 132 ETH (~$370k).
NFT marketplaces are important infrastructure for NFTs, and they will continue to grow in importance as demand for NFTs increases. These marketplaces are like eBay for NFTs. Owners can list their NFTs for sale, either as an auction or buy-it-now. Purchasers come in to bid on NFTs, and the marketplace’s smart contracts send the NFT to the winner’s wallet address. OpenSea is the most popular NFT marketplace for the secondary sale of NFTs. Other marketplaces curate special kinds of NFTs (e.g. Artblocks & AsyncArt), and host the NFT drops of popular artists (e.g. SuperRare & Nifty Gateway).
NFTs are much more than visual art. As I said before, any digital file can be made unique with NFTs, including audio, video, text, code, and more. Web3 music is up-and-coming where patrons can purchase one-of-a-kind, or limited edition songs on platforms like Catalog. Also, you can mint an NFT of your blog post on Mirror, which has been used for fundraising creative projects like documentaries among other things. Finally, some of the internets original source code, discussed in the first section of this article, was sold for $5.4 million dollars as an NFT. The list goes on.
Even digital media in general is just scratching the surface of NFT use-cases. NFTs can be programmed with arbitrary functionality. For example, NFTs can be used to give access to online communities like private Discord servers, or be used to access in-person events. Also, NFTs allow artists to capture royalties on secondary sales of their artwork without any legal contracts. The NFTs can be programmed in such a way that a percentage of secondary sales are automatically sent to the artist’s wallet address. We are just in the beginning stages of NFT experimentation – it’s not hard to imagine future use-cases where NFTs serve as our digital identities, or digital belongings that we carry with us through the Metaverse.
This brings us to the end of the Web3 Token module of the Web3 Design Course 2022. We learned how Web3 tokens are a disruptive force in that they incentivize open-source protocol develop, and align the economic interests of all stakeholders on cryptonetworks. These tokens are often sold to raise funds for the development of Web3 projects; however, the SEC considers this the sale of unregistered securities so we will see the rollout of regulatory frameworks to deal with Web3 tokens. Finally, there are two main types of Web3 tokens: fungible and non-fungible (NFTs). We are still in the early days of what these tokens are capable of. Many brilliant entrepreneurs are experimenting with various use-cases.
In the next course modules we will be doing deep-dives into the Web3 ecosystem. Everything before this has been meant to prepare you for understanding Web3 product categories like DeFi, Cryptomedia, Creator Tools, Social Media, Digital Identity, Data & AI/ML, GameFi, Metaverse, and Autonomous Organizations. Can’t wait to get into it!
Disclaimer
I, Travis Kassab, am not a financial advisor, tax professional, broker, or legal advisor. None of my podcasts, videos, or articles constitute financial advice. This content is purely for educational purposes, and is not intended to endorse any cryptocurrency or other investment vehicle. At the time of writing this, my cryptocurrency holdings include: BTC, ETH, CEL, SNX, BANK, SOL, DOT, KSM, USDC, GERO.
7 Comments
Open Source Software Mental Models | Web3 for UX Designers – designWeb3 · May 13, 2022 at 4:57 pm
[…] when it comes to online learning then checkout the course on YouTube. This is part 1 of 7 in the Crypto Design Trends 2022 series. Also, make sure to stay tuned for future Web3 Design Courses where we will get into more […]
Design History from Web1 to Web3 | Crypto Design Trends 2022 – designWeb3 · May 16, 2022 at 6:01 pm
[…] when it comes to online learning then checkout the course on YouTube. This is part 2 of 7 in the Crypto Design Trends 2022 series. Also, make sure to stay tuned for future Web3 Design Courses where we will get into more […]
Design Principles of Web3 Tokens | Crypto Design Trends 2022 – designWeb3 · May 18, 2022 at 4:21 pm
[…] when it comes to online learning then checkout the course on YouTube. This is part 3 of 7 in the Crypto Design Trends 2022 series. Also, make sure to stay tuned for future Web3 Design Courses where we will get into more […]
Design Thinking with Web3 Tokens | Crypto Design Trends 2022 – designWeb3 · May 20, 2022 at 4:20 pm
[…] when it comes to online learning then checkout the course on YouTube. This is part 4 of 7 in the Crypto Design Trends 2022 series. Also, make sure to stay tuned for future Web3 Design Courses where we will get into more […]
Designing Around SEC Regulation of Web3 Tokens | Crypto Design Trends 2022 – designWeb3 · May 25, 2022 at 4:12 pm
[…] when it comes to online learning then checkout the course on YouTube. This is part 6 of 7 in the Crypto Design Trends 2022 series. Also, make sure to stay tuned for future Web3 Design Courses where we will get into more […]
Design Principles of NFTs & Cryptomedia | Crypto Design Trends 2022 – designWeb3 · May 26, 2022 at 11:45 pm
[…] when it comes to online learning then checkout the course on YouTube. This is part 7 of 7 in the Crypto Design Trends 2022 series. Also, make sure to stay tuned for future Web3 Design Courses where we will get into more […]
DeFi for UX Designers | Web3 Design Bootcamp 2022 – designWeb3 · May 26, 2022 at 11:46 pm
[…] previous three design course modules (1, 2, 3) cover important background information on Web3. Now, we enter the Web3 ecosystem, starting with […]